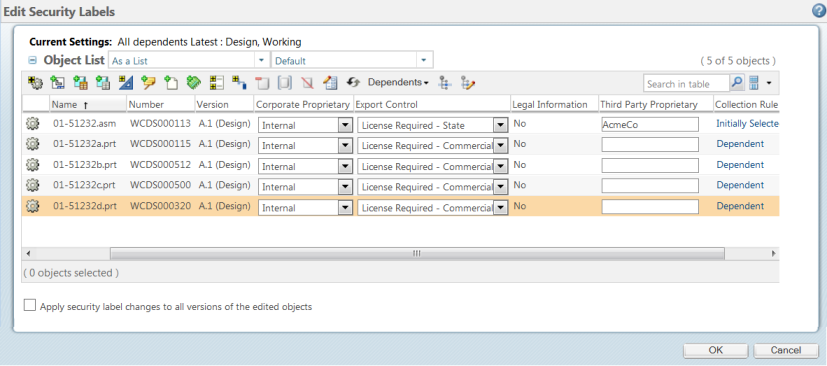
Edit Security Labels — Collect Related Objects
Use the Edit Security Labels action to modify the existing security label values on an object. If the object has related objects and collection rules are set, the Edit Security Labels window displays the object and any related objects in the Object List table. For more information about setting collection rules, see Collecting in Advanced Mode.
To change the security label values set on these objects, use the following procedure. For information on who can change security labels, see Viewing and Setting Security Labels on Existing Objects.
1. Select Edit Security Labels from:
◦ The right-click action menu for the object
◦ The Actions menu on the object information page
◦ The Actions menu on some tables
2. Collect any related objects using the actions available at the top of the Object List table. For more information, see Collecting in Advanced Mode.
You can view the objects in the Object List table in multiple ways, including as a list, as a structure, and so on. Select a display from the drop-down list next to the table title to change the way the objects are arranged in the table. You can also set the > > > preference to determine the default display type for the Object List table. For more information, see Preference Management and Setting a Preference. Out-of-the-box, a Default view is available from the Object List table from the Edit Security Labels window. The Default view includes columns for object status, object identity, and all configured security labels (including disabled security labels). Administrators or users can create new table views to limit the number of security label columns that appear in the Object List table. If certain users only need to see a subset of the configured security labels, an administrator can create and share a new view with those users that has columns for only certain security labels. For more information about creating new views, see Creating and Editing New Table Views, Administering Table Views for the Organization, and Administering Table Views for the Site. |
3. Set the desired security label values:
◦ On each object individually:
▪ For standard security labels, select the desired value from the drop-down list in the column for each security label.
▪ For standard security labels with multiple values, select the check boxes of the values from the drop-down list in the column for security label.
▪ For custom security labels, modify the value listed in the text box in the column for each security label.
◦ On several objects:
1. Select the checkbox next to the objects for which you want to set the same security label values.
2. Click the edit security label attribute values  icon.
icon.
3. Set the desired values. For more information, see Editing Attribute Values for Security Labels.
4. Click OK.
The Edit Attribute Values window closes and the updated security label values are reflected in the Object List table.
4. Select the Apply security label changes to all versions of the edited objects checkbox if you want changes applied to all versions of the object. Deselect the checkbox to apply changes to only the version you have selected. Your administrator may have configured your system to always apply changes to all versions or to only the current version, in which case a message is displayed stating how changes will be applied. For more information, see Before You Begin Configuring Security Labels
5. Click OK to save your changes and close the window.
When changing security label values, it is important to keep the following in mind: • Use care when setting security label values on an object. You can change the security label value to a value that restricts you from accessing the object after the change is applied. • If you clear all the values from the list and click OK, there is no change and the original values are retained. To set a Null value, select Null from the list. • If an object is checked out, be aware of whether you are changing security labels on the working copy or the original version of the object. Whether you are updating the working copy or the original copy of an object is determined by where the Edit Security Labels action was launched. For example, if you launch the Edit Security Labels action from the Checked-Out Work table, you are changing security labels on the working copy of the object. • If you are changing security labels on the original version of a checked out object instead of the working copy: ◦ The security labels in effect after the object is checked in will be those from the working copy. ◦ If you change a security label on the original object to a value that restricts access to the user who had the object checked out, then that user will be unable to check in the object. • It is not necessary for the object to be checked out to change security labels. If the only change you are making to the object is to change the security labels, do not check out the object. |